Geopolitical Risk and Digital Operations in the Middle East: A Deep Dive for Professionals
The Middle East, a region of immense strategic importance, is increasingly reliant on digital infrastructure. This reliance, however, makes it a prime target for geopolitical-driven cyberattacks and digital disruptions. To thrive in this environment, businesses must understand the unique risks and implement robust security strategies.
Introduction: The Complex Interplay of Geopolitics and Digital Security
Featured Snippet: Geopolitical risk significantly impacts digital operations in the Middle East due to regional instability, state-sponsored cyberattacks, and espionage. Businesses can navigate this uncertainty by implementing robust cybersecurity frameworks, threat intelligence, incident response plans, and by understanding local data sovereignty requirements.
The intersection of geopolitics and digital security is becoming increasingly critical, especially in regions like the Middle East. The region's complex political landscape, coupled with its growing digital economy, creates a volatile environment where businesses face a unique set of challenges. Understanding these challenges is the first step towards building a resilient digital operation.
Setting the Stage: Why the Middle East is a Digital Hotspot
The Middle East is experiencing rapid digital transformation. Smart city initiatives, widespread adoption of cloud technologies, and a burgeoning e-commerce sector are fueling this growth. However, this digital expansion also creates new vulnerabilities.
- High smartphone penetration rates (over 70% in many Gulf countries).
- Significant investments in smart infrastructure projects (estimated at $1 trillion by 2030).
- Growing reliance on cloud services for data storage and processing.
Defining Geopolitical Risk in the Digital Context
Geopolitical risk in the digital context refers to the potential for political events, international relations, and regional conflicts to negatively impact digital assets, operations, and infrastructure. This includes state-sponsored cyberattacks, espionage, disinformation campaigns, and regulatory changes driven by political motives.
- State-sponsored cyberattacks: Attacks orchestrated by nation-state actors to achieve political or economic objectives.
- Disinformation campaigns: The spread of false or misleading information to manipulate public opinion or destabilize governments.
- Regulatory changes: New laws and regulations that impact data privacy, cybersecurity, and digital trade.
The Growing Importance of Cybersecurity for Businesses in the Region
 Image: Pilots operating an aircraft cockpit during evening flight, showing illuminated control panels and distant coastline.
Image: Pilots operating an aircraft cockpit during evening flight, showing illuminated control panels and distant coastline.
Cybersecurity is no longer just an IT issue; it's a business imperative. The increasing frequency and sophistication of cyberattacks in the Middle East demand a proactive and comprehensive approach to security. According to a 2023 report by CrowdStrike, the Middle East saw a 47% increase in ransomware attacks compared to the previous year. This highlights the urgent need for enhanced cybersecurity measures.
- Protecting sensitive data: Preventing data breaches and protecting customer privacy.
- Ensuring business continuity: Maintaining operational resilience in the face of cyberattacks.
- Maintaining regulatory compliance: Adhering to local and international cybersecurity regulations.
Overview of Key Geopolitical Players and Their Digital Capabilities
Several key players influence the geopolitical landscape and digital security in the Middle East. Understanding their capabilities and motivations is crucial for assessing risk.
| Player | Digital Capabilities | Key Motivations | | ------------------- | -------------------------------------------------------------------------------------------------------------------------------------------------- | --------------------------------------------------------------------------------------------------------------- | | Iran | Advanced Persistent Threat (APT) groups with expertise in disruptive attacks and espionage. | Regional influence, cyber warfare capabilities, intelligence gathering. | | Saudi Arabia | Significant investments in cybersecurity infrastructure and defensive capabilities. | Protecting critical infrastructure, countering cyber threats, national security. | | Israel | Highly advanced cybersecurity industry and offensive capabilities. | Protecting national security, countering cyber threats, maintaining technological advantage. | | United Arab Emirates | Investing heavily in cybersecurity and artificial intelligence for both defensive and offensive purposes. | Protecting critical infrastructure, promoting economic growth, regional influence. | | Turkey | Growing cyber capabilities with a focus on espionage and influence operations. | Regional influence, intelligence gathering, protecting national interests. |
Understanding the Geopolitical Landscape: Key Risks to Digital Operations
The Middle East presents a complex web of geopolitical risks that can significantly impact digital operations. These risks range from state-sponsored cyberattacks to regulatory uncertainty.
State-Sponsored Cyberattacks: Identifying Actors and Motives
State-sponsored cyberattacks are a major threat in the Middle East. These attacks are often sophisticated, well-funded, and aimed at achieving specific political or economic objectives.
- Actors: Nation-state actors such as Iran, Saudi Arabia, Israel, and Turkey.
- Motives: Espionage, sabotage, intellectual property theft, and disruption of critical infrastructure.
- Examples: Attacks on energy companies, government agencies, and financial institutions. In 2012, Saudi Aramco was hit by the Shamoon virus, which wiped data from tens of thousands of computers.
Regional Conflicts and Their Impact on Digital Infrastructure
 Image: A military vehicle in an urban conflict environment in Al Hasakah, Syria.
Image: A military vehicle in an urban conflict environment in Al Hasakah, Syria.
Ongoing regional conflicts, such as the conflicts in Yemen and Syria, can have a significant impact on digital infrastructure. These conflicts can lead to physical damage to infrastructure, as well as cyberattacks targeting critical systems.
- Physical damage: Attacks on telecommunications infrastructure, power grids, and data centers.
- Cyberattacks: Targeting government networks, critical infrastructure, and businesses.
- Disruption of services: Internet outages, mobile network disruptions, and disruptions to online services.
Espionage and Intellectual Property Theft: Protecting Sensitive Data
Espionage and intellectual property theft are common threats in the Middle East. Nation-state actors and criminal organizations often target businesses to steal sensitive data, trade secrets, and intellectual property.
- Targets: Businesses in key sectors such as energy, finance, technology, and defense.
- Methods: Phishing attacks, malware infections, and social engineering.
- Consequences: Financial losses, reputational damage, and loss of competitive advantage.
Disinformation Campaigns and Their Effects on Public Opinion
Disinformation campaigns are increasingly used to manipulate public opinion and destabilize governments in the Middle East. These campaigns often rely on social media and online news platforms to spread false or misleading information.
- Objectives: Influencing elections, inciting social unrest, and undermining trust in institutions.
- Methods: Creating fake news websites, spreading propaganda on social media, and using bots to amplify messages.
- Impact: Erosion of public trust, polarization of society, and increased political instability.
Regulatory Uncertainty and Compliance Challenges
The regulatory landscape in the Middle East is constantly evolving, creating uncertainty and compliance challenges for businesses. Different countries have different laws and regulations regarding data privacy, cybersecurity, and digital trade.
- Data privacy laws: GDPR-like regulations in some countries, such as the UAE and Saudi Arabia.
- Cybersecurity regulations: Requirements for critical infrastructure protection and incident reporting.
- Digital trade regulations: Restrictions on cross-border data flows and e-commerce.
 Image: Operator in a modern control room managing technological systems in El Agustino, Lima.
Image: Operator in a modern control room managing technological systems in El Agustino, Lima.
Specific Threats and Vulnerabilities Facing Digital Operations
Digital operations in the Middle East face a range of specific threats and vulnerabilities. These threats can target critical infrastructure, data privacy, supply chains, and employees.
Critical Infrastructure Attacks: Targeting Energy, Telecom, and Finance
Critical infrastructure, such as energy, telecom, and finance, is a prime target for cyberattacks in the Middle East. These attacks can disrupt essential services and have a significant impact on the economy.
- Targets: Power grids, oil and gas pipelines, telecommunications networks, and financial institutions.
- Attack vectors: Malware infections, denial-of-service attacks, and physical sabotage.
- Consequences: Power outages, disruptions to telecommunications services, and financial losses.
Data Breaches and Privacy Concerns: Complying with Local Regulations
Data breaches are a growing concern in the Middle East, driven by the increasing volume of data being collected and stored online. Businesses must comply with local data privacy regulations to protect customer data and avoid penalties.
- Data privacy laws: Regulations such as the UAE's Federal Decree-Law No. 45 of 2021 on Personal Data Protection.
- Common causes: Weak passwords, unpatched vulnerabilities, and social engineering attacks.
- Consequences: Financial penalties, reputational damage, and loss of customer trust.
Supply Chain Vulnerabilities: Assessing and Mitigating Risks
Supply chain vulnerabilities can expose businesses to significant risks. Attackers can exploit weaknesses in a supplier's security to gain access to a company's network or data.
- Risks: Malware infections, data breaches, and disruptions to operations.
- Mitigation strategies: Conducting due diligence on suppliers, implementing security controls, and monitoring supplier activity.
- Example: A 2022 report by the SANS Institute found that 32% of organizations experienced a supply chain attack in the past year.
 Image: Close-up view of hands operating a drone controller outdoors at sunset.
Image: Close-up view of hands operating a drone controller outdoors at sunset.
Ransomware Attacks: Prevention, Detection, and Response
Ransomware attacks are a persistent threat in the Middle East. Attackers encrypt a victim's data and demand a ransom payment in exchange for the decryption key.
- Prevention: Implementing strong security controls, such as firewalls, intrusion detection systems, and endpoint protection.
- Detection: Monitoring network traffic for suspicious activity and using threat intelligence to identify potential attacks.
- Response: Developing an incident response plan and having backups of critical data.
Social Engineering and Phishing: Educating Employees and Strengthening Defenses
Social engineering and phishing attacks target employees to trick them into revealing sensitive information or clicking on malicious links. Educating employees and strengthening defenses are crucial for preventing these attacks.
- Training: Providing regular security awareness training to employees.
- Phishing simulations: Conducting simulated phishing attacks to test employee awareness.
- Technical controls: Implementing email filtering, multi-factor authentication, and endpoint protection.
Navigating the Uncertainty: Strategies for Mitigating Geopolitical Risks
Mitigating geopolitical risks requires a proactive and comprehensive approach. Businesses must develop a robust cybersecurity framework, implement threat intelligence, and develop incident response plans.
Developing a Robust Cybersecurity Framework: A Proactive Approach
A robust cybersecurity framework provides a structured approach to managing cybersecurity risks. This framework should be based on industry best practices and tailored to the specific needs of the organization.
- NIST Cybersecurity Framework: A widely used framework that provides guidance on identifying, protecting, detecting, responding to, and recovering from cyberattacks.
- ISO 27001: An international standard for information security management systems.
- Key elements: Risk assessment, security policies, access controls, incident response, and security awareness training.
 Image: A man burns a fake dollar with a Bitcoin symbol outdoors, symbolizing cryptocurrency risks.
Image: A man burns a fake dollar with a Bitcoin symbol outdoors, symbolizing cryptocurrency risks.
Implementing Threat Intelligence: Staying Ahead of Emerging Threats
Threat intelligence provides businesses with information about emerging threats and vulnerabilities. This information can be used to proactively defend against cyberattacks.
- Sources of threat intelligence: Security vendors, government agencies, and industry groups.
- Types of threat intelligence: Technical indicators, threat actor profiles, and vulnerability reports.
- Benefits: Improved threat detection, faster incident response, and reduced risk of cyberattacks.
Incident Response Planning: Preparing for the Inevitable
An incident response plan outlines the steps to be taken in the event of a cyberattack. This plan should be regularly tested and updated to ensure its effectiveness.
- Key elements: Incident identification, containment, eradication, recovery, and post-incident analysis.
- Roles and responsibilities: Clearly defined roles and responsibilities for incident response team members.
- Communication plan: A plan for communicating with stakeholders, including customers, employees, and regulators.
Data Localization and Sovereignty: Understanding Local Requirements
Data localization and sovereignty requirements mandate that certain types of data be stored and processed within a specific country. Businesses must understand and comply with these requirements to avoid legal and regulatory penalties.
- Regulations: Data localization laws in countries such as Saudi Arabia, the UAE and Qatar.
- Compliance strategies: Storing data in local data centers, using cloud providers with local presence, and implementing data encryption.
- Considerations: Cost, performance, and security.
Building Resilience and Redundancy: Ensuring Business Continuity
Building resilience and redundancy is crucial for ensuring business continuity in the face of cyberattacks or other disruptions. This includes implementing backup systems, disaster recovery plans, and business continuity plans.
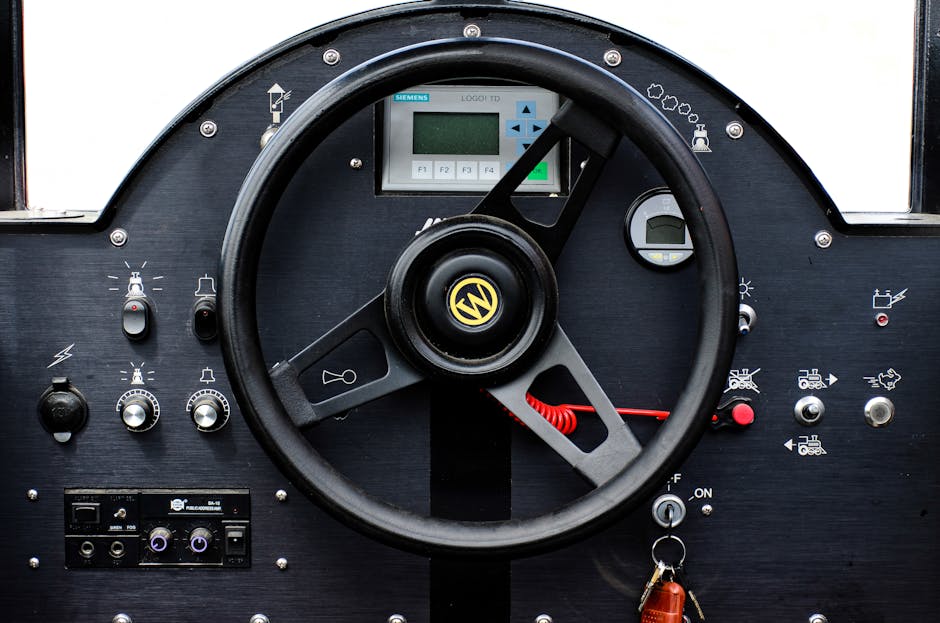 Image: Close-up of an industrial control dashboard with various buttons and a steering wheel.
Image: Close-up of an industrial control dashboard with various buttons and a steering wheel.
- Backup systems: Regularly backing up critical data and systems.
- Disaster recovery plans: Plans for recovering from a major disruption, such as a cyberattack or natural disaster.
- Business continuity plans: Plans for maintaining business operations during a disruption.
Real-World Examples: Case Studies of Geopolitical Risk Impacting Digital Operations
Analyzing real-world examples provides valuable insights into the impact of geopolitical risk on digital operations. The following case studies illustrate the challenges businesses face and the strategies they can use to mitigate these risks.
Case Study 1: The Impact of a Cyberattack on a Major Energy Company
In 2021, a major energy company in the Middle East was targeted by a sophisticated cyberattack attributed to a nation-state actor. The attack disrupted operations, leading to significant financial losses and reputational damage.
- Attack vector: A spear-phishing campaign targeting employees with access to critical systems.
- Impact: Disruption of oil and gas production, financial losses estimated at $50 million, and reputational damage.
- Lessons learned: The importance of employee security awareness training, implementing multi-factor authentication, and monitoring network traffic for suspicious activity.
Case Study 2: How Geopolitical Tensions Led to a Data Breach in the Financial Sector
In 2022, a financial institution in the Middle East experienced a data breach that compromised the personal information of millions of customers. The breach was attributed to a cyber espionage campaign linked to geopolitical tensions in the region.
- Attack vector: A vulnerability in a third-party software application.
- Impact: Loss of customer data, financial penalties, and reputational damage.
- Lessons learned: The importance of third-party risk management, vulnerability management, and incident response planning.
Case Study 3: Successfully Navigating Regulatory Challenges in the UAE
A multinational technology company successfully navigated regulatory challenges in the UAE by proactively engaging with regulators and implementing robust data privacy and cybersecurity measures.
 Image: A rescue worker in Phú Yên, Vietnam, aids flood victims during nighttime operations.
Image: A rescue worker in Phú Yên, Vietnam, aids flood victims during nighttime operations.
- Strategy: Establishing a local presence, engaging with regulators, and complying with local data privacy and cybersecurity regulations.
- Outcome: Successful market entry and expansion in the UAE.
- Lessons learned: The importance of understanding local regulations, building relationships with regulators, and implementing robust compliance programs.
Analysis of Lessons Learned from These Incidents
These case studies highlight the importance of a proactive and comprehensive approach to managing geopolitical risks. Businesses must invest in cybersecurity, implement threat intelligence, develop incident response plans, and comply with local regulations.
- Proactive security: Implementing strong security controls to prevent cyberattacks.
- Threat intelligence: Staying ahead of emerging threats by monitoring threat intelligence feeds.
- Incident response: Having a plan in place to respond to cyberattacks.
- Regulatory compliance: Complying with local data privacy and cybersecurity regulations.
Expert commentary on the case studies.
"These cases underscore that in the Middle East, cybersecurity is inextricably linked to geopolitics. Organizations must move beyond generic security practices and adopt a threat-informed approach. Understanding the motivations and capabilities of regional actors is paramount," says Dr. Aisha Al-Mansoori, a leading cybersecurity expert at Khalifa University. "Furthermore, these incidents highlight the critical need for collaboration between the public and private sectors to share threat intelligence and coordinate incident response efforts."
Future Trends: The Evolving Geopolitical Landscape and its Implications for Digital Security
The geopolitical landscape is constantly evolving, and businesses must stay ahead of emerging trends to protect their digital operations. Key trends include the rise of artificial intelligence in cyber warfare, the increasing importance of digital diplomacy, and the impact of 5G on critical infrastructure security.
The Rise of Artificial Intelligence in Cyber Warfare
Artificial intelligence (AI) is increasingly being used in cyber warfare, both for offensive and defensive purposes. AI can be used to automate attacks, identify vulnerabilities, and improve threat detection.
- Offensive uses: AI-powered malware, automated phishing attacks, and autonomous cyber weapons.
- Defensive uses: AI-powered threat detection, automated incident response, and vulnerability management.
- Implications: Increased sophistication of cyberattacks, faster attack cycles, and the need for AI-powered security solutions.
 Image: Close-up of a drone controller held by a person with a smartphone displaying aerial footage.
Image: Close-up of a drone controller held by a person with a smartphone displaying aerial footage.
The Increasing Importance of Digital Diplomacy
Digital diplomacy is becoming increasingly important as governments use digital platforms to communicate with each other and with the public. Digital diplomacy can be used to resolve conflicts, promote cooperation, and counter disinformation.
- Tools: Social media, online forums, and video conferencing.
- Objectives: Building relationships, promoting dialogue, and countering disinformation.
- Implications: Increased transparency, faster communication, and the potential for digital conflict resolution.
The Impact of 5G on Critical Infrastructure Security
5G technology is transforming critical infrastructure, enabling new applications and services. However, 5G also introduces new security vulnerabilities.
- Benefits: Faster speeds, lower latency, and increased capacity.
- Vulnerabilities: Increased attack surface, supply chain risks, and reliance on software.
- Implications: The need for enhanced security measures to protect 5G networks and critical infrastructure.
Predicting Future Geopolitical Flashpoints and Their Digital Impact
Predicting future geopolitical flashpoints is challenging, but businesses can use risk analysis and scenario planning to prepare for potential disruptions. Key areas to watch include:
- Regional conflicts: Ongoing conflicts in Yemen, Syria, and Libya.
- Political instability: Elections and political transitions in key countries.
- Economic tensions: Trade disputes and economic sanctions.
- Cyber warfare: Escalation of cyberattacks between nation-state actors.
Recommendations for Long-Term Planning and Adaptation
Businesses must develop long-term plans and adapt to the evolving geopolitical landscape. This includes:
- Investing in cybersecurity: Allocating sufficient resources to cybersecurity.
- Implementing threat intelligence: Staying ahead of emerging threats.
- Developing incident response plans: Preparing for cyberattacks.
- Building resilience: Ensuring business continuity.
- Engaging with stakeholders: Collaborating with governments, industry groups, and security vendors.
FAQ: Addressing Common Concerns about Geopolitical Risk and Digital Operations in the Middle East
Here are some frequently asked questions about geopolitical risk and digital operations in the Middle East:
What are the biggest geopolitical risks facing digital operations in the Middle East?
The biggest risks include state-sponsored cyberattacks, regional conflicts impacting digital infrastructure,